2020. 2. 22. 09:42ㆍ카테고리 없음
Active Directory ( AD) is a developed by for networks. It is included in most as a set of. Initially, Active Directory was only in charge of centralized domain management. Starting with, however, Active Directory became an umbrella title for a broad range of directory-based identity-related services.A server running Active Directory Domain Service (AD DS) is called a. It and all users and computers in a Windows domain type network—assigning and enforcing security policies for all computers and installing or updating software. For example, when a user a computer that is part of a Windows domain, Active Directory checks the submitted password and determines whether the user is a or normal user.
Also, it allows management and storage of information, provides authentication and authorization mechanisms, and establishes a framework to deploy other related services: Certificate Services, Lightweight Directory Services and.Active Directory uses (LDAP) versions 2 and 3, Microsoft's version of,. Contents.History Active Directory, like many information-technology efforts, originated out of a using or RFCs. The (IETF), which oversees the RFC process, has accepted numerous RFCs initiated by widespread participants. Active Directory incorporates decades of communication technologies into the overarching Active Directory concept then makes improvements upon them. For example, LDAP underpins Active Directory. Also directories and the preceded the Active Directory concept that makes use of those methods. The LDAP concept began to emerge even before the founding of Microsoft in April 1975, with RFCs as early as 1971.
RFCs contributing to LDAP include (on the LDAP API, August 1995), and.Microsoft previewed Active Directory in 1999, released it first with Server edition, and revised it to extend functionality and improve administration in. Additional improvements came with subsequent versions of.
In, additional services were added to Active Directory, such as. The part of the directory in charge of management of domains, which was previously a core part of the operating system, was renamed Active Directory Domain Services (ADDS) and became a server role like others. 'Active Directory' became the umbrella title of a broader range of directory-based services. According to Bryon Hynes, everything related to identity was brought under Active Directory's banner. Active Directory Services Active Directory Services consist of multiple directory services.
The best known is Active Directory Domain Services, commonly as AD DS or simply AD. Domain Services Active Directory Domain Services (AD DS) is the cornerstone of every network. It stores information about members of the domain, including devices and users,. The server running this service is called a. A domain controller is contacted when a user logs into a device, accesses another device across the network, or runs a line-of-business into a device.Other Active Directory services (excluding, as described below) as well as most of Microsoft server technologies rely on or use Domain Services; examples include, and.Lightweight Directory Services Active Directory Lightweight Directory Services ( AD LDS), formerly known as Active Directory Application Mode (ADAM), is a light-weight implementation of AD DS. AD LDS runs as a on. AD LDS shares the code base with AD DS and provides the same functionality, including an identical, but does not require the creation of domains or domain controllers.
It provides a Data Store for storage of directory data and a with an LDAP Directory Service Interface. Unlike AD DS, however, multiple AD LDS instances can run on the same server.Certificate Services Active Directory Certificate Services (AD CS) establishes an on-premises. It can create, validate and revoke for internal uses of an organization. These certificates can be used to encrypt files (when used with ), emails (per standard), and network traffic (when used by, protocol or protocol).AD CS predates Windows Server 2008, but its name was simply Certificate Services.AD CS requires an AD DS infrastructure.
Federation Services. Main article:Active Directory Federation Services (AD FS) is a service. With an AD FS infrastructure in place, users may use several web-based services (e.g., ) or network resources using only one set of credentials stored at a central location, as opposed to having to be granted a dedicated set of credentials for each service. AD FS's purpose is an extension of that of AD DS: The latter enables users to authenticate with and use the devices that are part of the same network, using one set of credentials.
The former enables them to use the same set of credentials in a different network.As the name suggests, AD FS works based on the concept of.AD FS requires an AD DS infrastructure, although its federation partner may not. Rights Management Services. Main article:Active Directory Rights Management Services ( AD RMS, known as Rights Management Services or RMS before ) is a server software for shipped with. It uses encryption and a form of selective functionality denial for limiting access to documents such as corporate, documents, and, and the operations authorized users can perform on them.Logical structure As a directory service, an Active Directory instance consists of a database and corresponding responsible for servicing requests and maintaining the database.
The executable part, known as Directory System Agent, is a collection of and that run on Windows 2000 and later. Objects in Active Directory databases can be accessed via LDAP, ADSI (a interface), and services. A simplified example of a publishing company's internal network. The company has four groups with varying permissions to the three shared folders on the network.Active Directory structures are arrangements of information about. The objects fall into two broad categories: resources (e.g., printers) and (user or computer accounts and groups). Security principals are assigned unique (SIDs).Each object represents a single entity—whether a user, a computer, a printer, or a group—and its attributes. Certain objects can contain other objects.
An object is uniquely identified by its name and has a set of attributes—the characteristics and information that the object represents— defined by a, which also determines the kinds of objects that can be stored in Active Directory.The lets administrators extend or modify the schema when necessary. However, because each schema object is integral to the definition of Active Directory objects, deactivating or changing these objects can fundamentally change or disrupt a deployment. Schema changes automatically propagate throughout the system. Once created, an object can only be deactivated—not deleted. Changing the schema usually requires planning.
Forests, trees and domains The Active Directory framework that holds the objects can be viewed at a number of levels. The forest, tree, and domain are the logical divisions in an Active Directory network.Within a deployment, objects are grouped into domains. The objects for a single domain are stored in a single database (which can be replicated).
Domains are identified by their name structure, the.A domain is defined as a logical group of network objects (computers, users, devices) that share the same Active Directory database.A tree is a collection of one or more domains and domain trees in a contiguous namespace, and is linked in a transitive trust hierarchy.At the top of the structure is the forest. A forest is a collection of trees that share a common global catalog, directory schema, logical structure, and directory configuration. The forest represents the security boundary within which users, computers, groups, and other objects are accessible.Domain-BostonDomain-New YorkDomain-PhillyTree-SouthernDomain-AtlantaDomain-DallasDomain-DallasOU-MarketingHewittAonSteveOU-SalesBillRalphExample of the geographical organizing of zones of interest within trees and domains.Organizational units The objects held within a domain can be grouped into (OUs). OUs can provide hierarchy to a domain, ease its administration, and can resemble the organization's structure in managerial or geographical terms. OUs can contain other OUs—domains are containers in this sense. Microsoft recommends using OUs rather than domains for structure and to simplify the implementation of policies and administration.
The OU is the recommended level at which to apply, which are Active Directory objects formally named Group Policy Objects (GPOs), although policies can also be applied to domains or sites (see below). The OU is the level at which administrative powers are commonly delegated, but delegation can be performed on individual objects or attributes as well.Organizational units do not each have a separate namespace.
As a consequence, for compatibility with Legacy NetBios implementations, user accounts with an identical sAMAccountName are not allowed within the same domain even if the accounts objects are in separate OUs. This is because sAMAccountName, a user object attribute, must be unique within the domain. However, two users in different OUs can have the same Common Name (CN), the name under which they are stored in the directory itself such as 'fred.staff-ou.domain' and 'fred.student-ou.domain', where 'staff-ou' and 'student-ou' are the OUs.In general the reason for this lack of allowance for duplicate names through hierarchical directory placement, is that Microsoft primarily relies on the principles of, which is a flat-file method of network object management that for Microsoft software, goes all the way back to. Allowing for duplication of object names in the directory, or completely removing the use of NetBIOS names, would prevent backward compatibility with legacy software and equipment.
However, disallowing duplicate object names in this way is a violation of the LDAP RFCs on which Active Directory is supposedly based.As the number of users in a domain increases, conventions such as 'first initial, middle initial, last name' or the reverse (Eastern order) fail for common like Li (李), Smith or Garcia. Workarounds include adding a digit to the end of the username. Alternatives include creating a separate ID system of unique employee/student id numbers to use as account names in place of actual user's names, and allowing users to nominate their preferred word sequence within an.Because duplicate usernames cannot exist within a domain, account name generation poses a significant challenge for large organizations that cannot be easily subdivided into separate domains, such as students in a public school system or university who must be able to use any computer across the network.Shadow groups. In Active Directory, organizational units (OUs) cannot be assigned as owners or trustees.
Only groups are selectable, and members of OUs cannot be collectively assigned rights to directory objects.In Microsoft's Active Directory, OUs do not confer access permissions, and objects placed within OUs are not automatically assigned access privileges based on their containing OU. This is a design limitation specific to Active Directory. Other competing directories such as Novell are able to assign access privileges through object placement within an OU.Active Directory requires a separate step for an administrator to assign an object in an OU as a member of a group also within that OU. Relying on OU location alone to determine access permissions is unreliable, because the object may not have been assigned to the group object for that OU.A common workaround for an Active Directory administrator is to write a custom or script to automatically create and maintain a user group for each OU in their directory. The scripts are run periodically to update the group to match the OU's account membership, but are unable to instantly update the security groups anytime the directory changes, as occurs in competing directories where security is directly implemented into the directory itself. Such groups are known as Shadow Groups.
Once created, these shadow groups are selectable in place of the OU in the administrative tools.Microsoft refers to shadow groups in the Server 2008 Reference documentation, but does not explain how to create them. There are no built-in server methods or console snap-ins for managing shadow groups.The division of an organization's information infrastructure into a hierarchy of one or more domains and top-level OUs is a key decision. Common models are by business unit, by geographical location, by IT Service, or by object type and hybrids of these. OUs should be structured primarily to facilitate administrative delegation, and secondarily, to facilitate group policy application. Although OUs form an administrative boundary, the only true security boundary is the forest itself and an administrator of any domain in the forest must be trusted across all domains in the forest.
Partitions The Active Directory database is organized in partitions, each holding specific object types and following a specific replication pattern. Microsoft often refers to these partitions as 'naming contexts'.
The 'Schema' partition contains the definition of object classes and attributes within the Forest. The 'Configuration' partition contains information on the physical structure and configuration of the forest (such as the site topology). Both replicate to all domains in the Forest. The 'Domain' partition holds all objects created in that domain and replicates only within its domain.Physical structure Sites are physical (rather than logical) groupings defined by one or more subnets.
AD also holds the definitions of connections, distinguishing low-speed (e.g., ) from high-speed (e.g., ) links. Site definitions are independent of the domain and OU structure and are common across the forest. Sites are used to control network traffic generated by replication and also to refer clients to the nearest (DCs).
Uses the site topology for mail routing. Policies can also be defined at the site level.Physically, the Active Directory information is held on one or more peer, replacing the / model.
Each DC has a copy of the Active Directory. Servers joined to Active Directory that are not domain controllers are called Member Servers. A subset of objects in the domain partition replicate to domain controllers that are configured as global catalogs. Global catalog (GC) servers provide a global listing of all objects in the Forest.Global Catalog servers replicate to themselves all objects from all domains and hence, provide a global listing of objects in the forest. However, to minimize replication traffic and keep the GC's database small, only selected attributes of each object are replicated. This is called the partial attribute set (PAS).
The PAS can be modified by modifying the schema and marking attributes for replication to the GC. Earlier versions of Windows used to communicate. Active Directory is fully integrated with DNS and requires —DNS. To be fully functional, the DNS server must support, also known as service records.Replication Active Directory synchronizes changes using. Replication by default is 'pull' rather than 'push', meaning that replicas pull changes from the server where the change was effected.
The Knowledge Consistency Checker (KCC) creates a replication topology of site links using the defined sites to manage traffic. Intrasite replication is frequent and automatic as a result of change notification, which triggers peers to begin a pull replication cycle. Intersite replication intervals are typically less frequent and do not use change notification by default, although this is configurable and can be made identical to intrasite replication.Each link can have a 'cost' (e.g., etc.) and the KCC alters the site link topology accordingly.
Replication may occur transitively through several site links on same-protocol site link bridges, if the cost is low, although KCC automatically costs a direct site-to-site link lower than transitive connections. Site-to-site replication can be configured to occur between a bridgehead server in each site, which then replicates the changes to other DCs within the site. Replication for Active Directory zones is automatically configured when DNS is activated in the domain based by site.Replication of Active Directory uses (RPC) over IP (RPC/IP). Between Sites can be used for replication, but only for changes in the Schema, Configuration, or Partial Attribute Set (Global Catalog) GCs. SMTP cannot be used for replicating the default Domain partition.
Implementation In general, a network utilizing Active Directory has more than one licensed Windows server computer. Backup and restore of Active Directory is possible for a network with a single domain controller, but Microsoft recommends more than one domain controller to provide automatic protection of the directory. Domain controllers are also ideally single-purpose for directory operations only, and should not run any other software or role.Certain Microsoft products such as SQL Server and Exchange can interfere with the operation of a domain controller, necessitating isolation of these products on additional Windows servers. Combining them can make configuration or troubleshooting of either the domain controller or the other installed software more difficult. Retrieved 23 April 2014. ^; (2005).
'Chapter 13'. Redmond, Washington:. P. 840. ^ Hynes, Byron (November 2006).
Active Directory Collection. 13 March 2003. Retrieved 25 December 2010. 27 April 2016. Retrieved 22 September 2016.
Retrieved 26 November 2013. Retrieved 26 November 2013. Retrieved 26 November 2013.
Retrieved 26 November 2013. ^ Thomas, Guy. Computer Performance Ltd. Windows Server 2012 R2 and Windows Server 2012 Tech Center. Retrieved 28 April 2009. Retrieved 25 February 2013. Zacker, Craig (2003).
'11: Creating and Managing Digital Certificates'. In Harding, Kathy; Jean, Trenary; Linda, Zacker (eds.). Redmond, WA: Microsoft Press. Retrieved 24 November 2015. Retrieved 24 November 2015. Windows Server 2003: Active Directory Infrastructure.
Microsoft Press. Distributed Systems Resource Kit.
Adjara
An organizational unit in Active Directory is analogous to a directory in the file system. 4 January 2012.
Retrieved 18 September 2013. Examples of how multiple AD objects can be created with the same sAMAccountName. Microsoft Server 2008 Reference, discussing shadow groups used for fine-grained password policies:. Microsoft Corporation. 23 January 2005. However, service administrators have abilities that cross domain boundaries.
For this reason, the forest is the ultimate security boundary, not the domain. Andreas Luther. Microsoft Corporation. Retrieved 26 May 2010.
The Active Directory is made up of one or more naming contexts or partitions. Microsoft Corporation. 21 January 2005. A site is a set of well-connected subnets. Microsoft Corporation.
21 January 2005. member servers,. belong to a domain but do not contain a copy of the Active Directory data.
Microsoft Corporation. 10 December 2009. a domain controller can locate only the objects in its domain.
The global catalog provides the ability to locate objects from any domain. Microsoft Corporation. Microsoft Corporation. 26 August 2010. The isMemberOfPartialAttributeSet attribute of an attributeSchema object is set to TRUE if the attribute is replicated to the global catalog. When deciding whether or not to place an attribute in the global catalog remember that you are trading increased replication and increased disk storage on global catalog servers for, potentially, faster query performance. Microsoft Corporation.
21 January 2005. Active Directory uses four distinct directory partition types to store. data. Directory partitions contain domain, configuration, schema, and application data.
Microsoft Corporation. 28 March 2003. Domain controllers request (pull) changes rather than send (push) changes that might not be needed. Microsoft Corporation. 28 March 2003. SMTP can be used to transport nondomain replication.
Adjaranet
Retrieved 5 February 2014. Retrieved 5 February 2014. Posey, Brien (23 August 2010). Retrieved 5 February 2014. Whenever possible, your domain controllers should run on dedicated servers (physical or virtual).
7 January 2013. Retrieved 5 February 2014.
Degremont, Michel (30 June 2011). Microsoft SQL Server blog. Retrieved 5 February 2014.
For security and performance reasons, we recommend that you do not install a standalone SQL Server on a domain controller. 22 March 2013. Retrieved 5 February 2014. Retrieved 5 February 2014. After SQL Server is installed on a computer, you cannot change the computer from a domain controller to a domain member.
You must uninstall SQL Server before you change the host computer to a domain member. Retrieved 5 February 2014. Running SQL Server on the same computer as a production Exchange mailbox server is not recommended.
Planning to Virtualize Domain Controllers. Retrieved 5 February 2014. You should attempt to avoid creating potential single points of failure when you plan your virtual domain controller deployment.frank. ^ efleis (8 June 2006).
Retrieved 20 November 2011. Berkouwer, Sander., Microsoft.
Microsoft Corporation. 28 March 2003.
Trusts enable. authentication and. sharing resources across domains or forests.
Microsoft Corporation. 11 December 2012. Retrieved 29 January 2013. Defines several kinds of trusts.
(automatic, shortcut, forest, realm, external). ^ Edge, Charles S., Jr; Smith, Zack; Hunter, Beau (2009). 'Chapter 3: Active Directory'. Enterprise Mac Administrator's Guide. New York City:. SAMBA Project.
From the original on 15 November 2010. Retrieved 9 August 2016. SAMBA Project.

5 October 2009. Archived from on 13 October 2009. Retrieved 2 November 2009. Archived from on 27 September 2011. Retrieved 20 November 2011.
Retrieved 7 June 2011. Retrieved 22 May 2012. Retrieved 22 May 2012. Perl Open-Source Community. Retrieved 22 May 2012.External links Wikiversity has learning resources about. Microsoft Technet: White paper: (Single technical document that gives an overview about Active Directory.).
Microsoft Technet: Detailed description of. Microsoft MSDN Library: (part of the ).
Microsoft MSDN:. Microsoft TechNet:. Microsoft MSDN:.
Microsoft TechNet:. Microsoft TechNet Magazine:. Microsoft MSDN:. Microsoft TechNet.
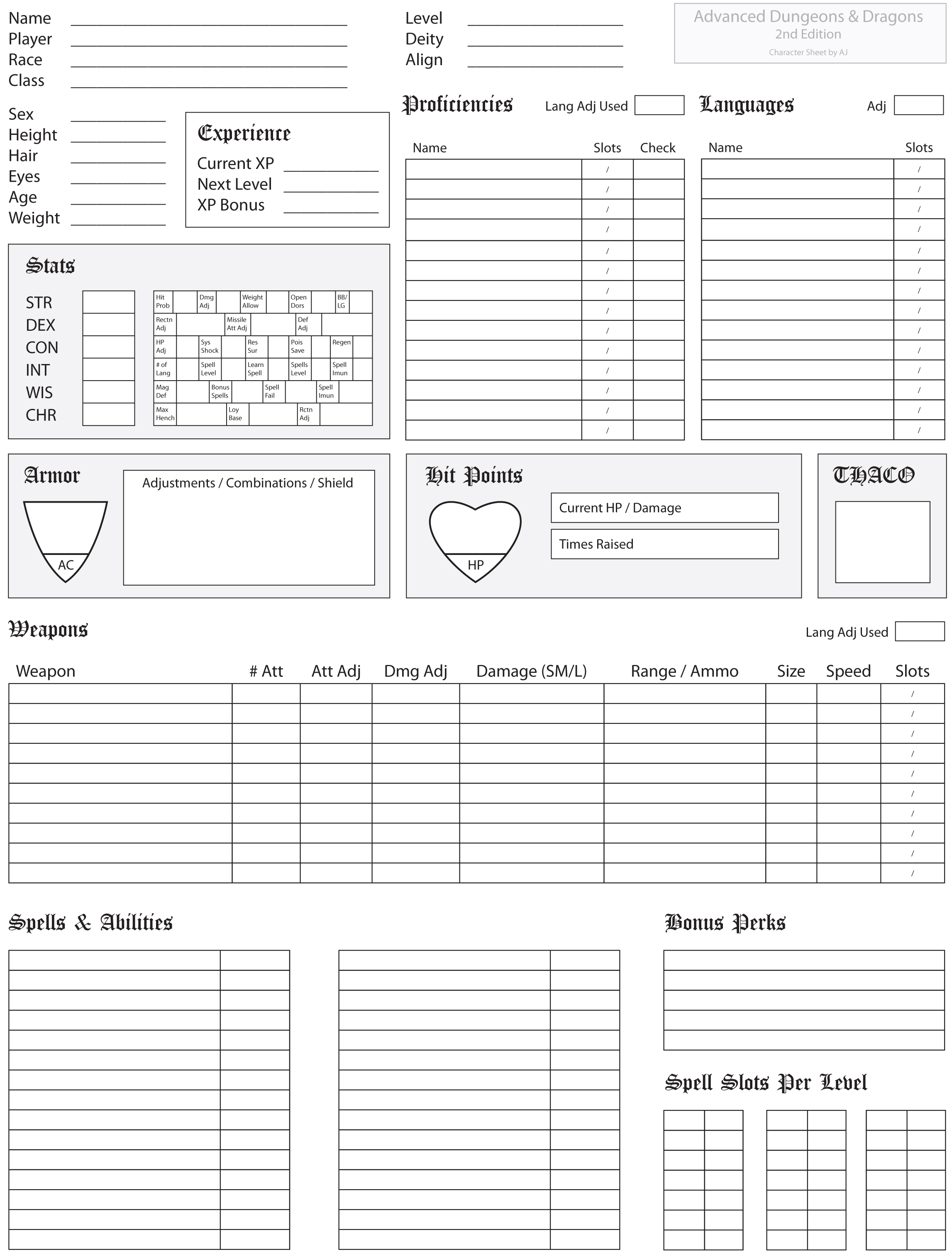
Ego is the mystical driving force that makes the character a uniqueindividual. Ego is divided into the subabilities of Willpower,which measures a characters strength of will and commitment andAura, which measure a characters spiritual strength, life energyor inner essence, and luck. Leon decides his character has averageWillpower.
The characters statistics now read:Strength 16Intelligence 12Stamina 15Knowledge 12Muscle 17Reason 11Dexterity 14Wisdom 8Aim 12Intuition 10Balance 16Understanding 6Constitution 12Charisma 11Health 12Leadership 10Fitness 12Appearance 12Ego 13Willpower 11Aura 15. Other affects of Ego: Ego affects a PCs ability to control intelligent magic weapons.The formula for determining the PC's power rating vs. Intelligentmagical items follows: Intelligence + Level + Ego.WillpowerThis ability measures a characters strength of will, abilityto resist magical forces, and sense of commitment to a cause.A character with a high Willpower would be difficult to harm withmind-affecting magic spells, could be quite stubborn, and wouldresist interrogation.Magical Defense Adjustment: This modifier applies to the character's saving throws versus magical spells that affect the victim's mind beguiling, charm, fear, hypnosis, possession, suggestion, etc. This modifier is applied automatically, without any effort on the part of the character or player making the saving throw.Spell Immunity: This grants those characters with extremely high Willpower scores protection from mind-affecting spells and psionic devotions and sciences which attack the characters mind.Skills: This ability is important for skills such as Animal handling, Animal training, Concentration and Intimidation. Table 1.13: WillpowerAbility ScoreMental Attack Adjust.Attack Immunity1-6nil2-5nil3-4nil4-3nil5-2nil6-1nil7-140nil15+1nil16+2nil17+3nil18+4nil19+41st level spells20+42nd level spells21+43rd level spells22+44th level spells23+45th level spells24+46th level spells and psionic devotions25+47th level spells and psionic sciencesAuraThis ability measures the strength of a characters life force,luck and ability to resist magic which affects the characterslife energy, such as necromantic spells. A character with a highAura has a powerful life energy and is less effected by the lifesapping attacks of undead and the effects of death magic. A characterwith a high Aura has a greater potential to use his mind to harnesspsionic powers and may also be very lucky.Life Point Bonus: This is the number of additional life points a character receives in addition to those awarded by race and level.Luck Point Bonus: This is the number of luck points a character receives in addition to those awarded by levelDeath Magic Defense Adjustment: This is the bonus a character receives to his saving throw vs.
Death magic and necromantic spells. The saving throw bonus can be ignored by a character who wishes to be affected by a spell.Skills: This ability is important for skills such as Meditative Focus, Rejuvenation and Spirit Lore.